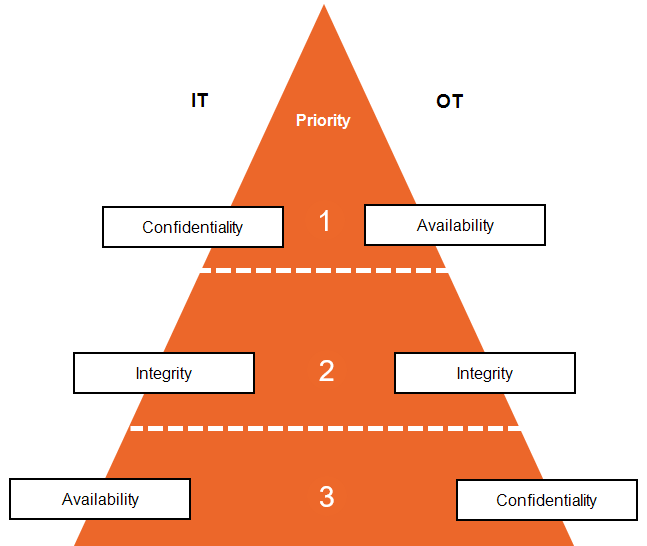
How Security Priorities Differ Between IT and IACS Environments
Operational Technology (OT) serves as the broad umbrella for managing physical systems, utilizing Information Technology (IT) and Industrial Automation and Control Systems (IACS) as the foundational framework for automation and security, which is typically deployed via SCADA for geographically distributed assets or DCS for integrated, localized process control.
Considering the growing shift in cyber threats affecting OT, it is essential to understand how security priorities differ between IT and IACS environments. This distinction directly influences how organizations should design, implement and respond to Cybersecurity risks in OT environments:
-
IT departments prioritize confidentiality, integrity and availability.
-
IACS security typically prioritize availability, integrity and confidentiality, this is because disruptions to availability or integrity in industrial environments can have immediate and potentially catastrophic consequences for safety, equipment and production.
Although both IT and OT aim to protect systems and data, the order of importance reflects their distinct operating contexts and risk profiles:
In the context of IACS, cybersecurity efforts generally fall into three essential categories:
- Prevention - Implementing controls to reduce the likelihood of incidents, for example, unauthorized access, data tampering or system compromise.
- Detection - Monitoring systems to identify when a security event occurs and collect relevant data for investigation.
- Response and Recovery - Taking appropriate action to contain and mitigate any impact of the incident, restore operations and prevent recurrence.
Last update - February 2026