How Attackers Attack
Depending on motives and skills, an attacker may or may not need to know the details of a control process to disrupt operations. For example, if the motive is simply to shut down the process, they need very little knowledge. However, if an attacker wants to attack a specific machine or process, they need to understand the application program.
Highly vulnerable processes include but are not limited to:
-
Data acquisition databases - Names of databases vary from supplier to supplier but a majority use a common naming convention with a unique number, for example, pump1, pump2, furnace1, breaker2. On the communications protocol level, the devices are simply referred to by number, memory location or register address. For a precise attack, the attacker must translate the numbers into meaningful information.
-
Human Machine Interfaces (HMI) or Supervisory Control and Data acquisition (SCADA) display screens - Gaining access to an HMI
 The user interface of a device, for example, a keypad, screen or mouse screen is one method for understanding a process and the interaction between an operator and the equipment. The information on the screen allows an attacker to translate the reference numbers into something meaningful.
The user interface of a device, for example, a keypad, screen or mouse screen is one method for understanding a process and the interaction between an operator and the equipment. The information on the screen allows an attacker to translate the reference numbers into something meaningful. -
Infection of equipment - All devices use software to operate. This could be in the form of an operating system, for example, Microsoft Windows, or any firmware or operating system used in network equipment, a SCADA system, programmable automation controllers (PAC)s or cameras. If an attacker manages to modify this software, access to information is easy and very difficult to detect.
In the ICS-CERT Monitor April/May/June 2013 issue, it was reported that they received a report from a gas compressor station owner on February 22nd 2013, about increased brute force attempts to access their process control network![]() The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic. The Stuxnet virus is one the most well-known, largest and successful industrial attack reported, it was used to target PLC systems in Iran's nuclear program.
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic. The Stuxnet virus is one the most well-known, largest and successful industrial attack reported, it was used to target PLC systems in Iran's nuclear program.
Select from the options below to display the details required:
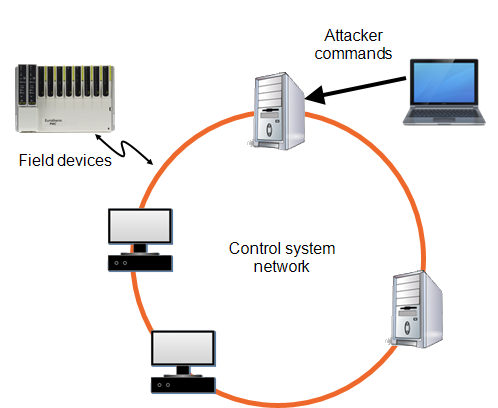
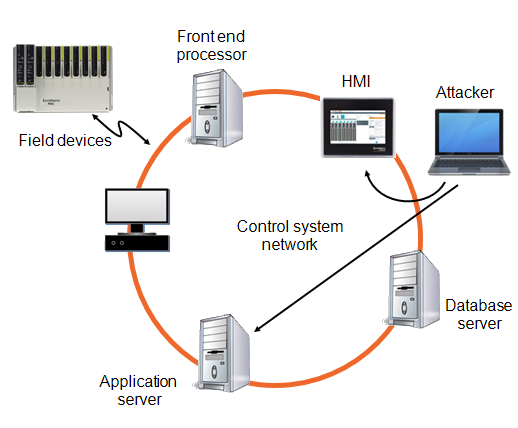
Once an attacker has enough information about a process, the next step is to manipulate it. One way to gain control of a process is to connect to a data acquisition device, for example, a programmable automation controller (PAC) that has access to field devices and send it properly formatted commands. Many PACs, gateways![]() A combination of hardware and software that interconnects incompatible networks or networking devices. Gateways include, packet assembler/disassembler and protocol converters and data acquisition servers use weak or no authentication and accept any commands that are formatted correctly:
A combination of hardware and software that interconnects incompatible networks or networking devices. Gateways include, packet assembler/disassembler and protocol converters and data acquisition servers use weak or no authentication and accept any commands that are formatted correctly:
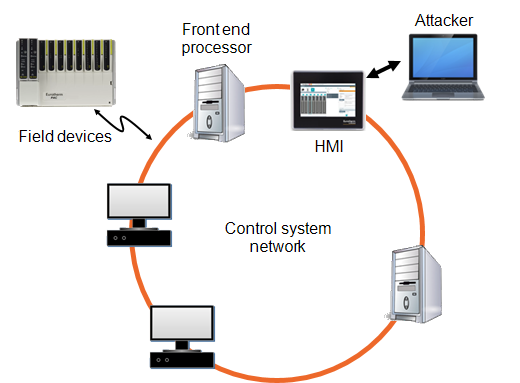
An attack could export a human machine interface (HMI![]() The user interface of a device, for example, a keypad, screen or mouse) screen to gain control of operations. If an attacker succeeds, they can view an operator's HMI screen and control it from their screen. A sophisticated attacker may also modify the operator's screen to display normal operations to disguise an attack:
The user interface of a device, for example, a keypad, screen or mouse) screen to gain control of operations. If an attacker succeeds, they can view an operator's HMI screen and control it from their screen. A sophisticated attacker may also modify the operator's screen to display normal operations to disguise an attack:
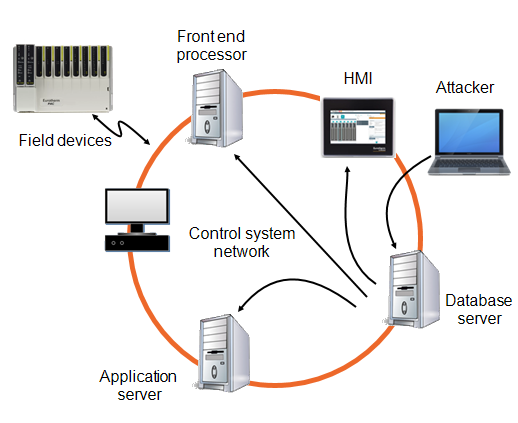
A successful attack can access a database and modify the data to disrupt normal operation of a control system, or change stored values to affect the system's integrity:
A man-in-the-middle (MITM) is a type of attack where an attacker intercepts messages from one computer (Host A), manipulates the data, and then forwards it to the intended computer (Host B). Both computers appear to be communicating with each other and neither system detects the presence of an intruder in the middle:
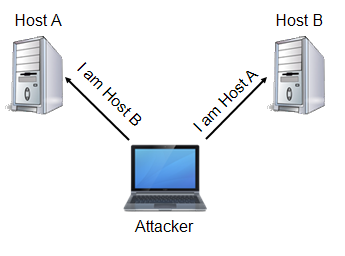
A MITM attack can even allow the attacker to fake the operator human machine interfaces (HMI![]() The user interface of a device, for example, a keypad, screen or mouse) screens and take control of a control system. For an attack to succeed, an attacker needs to know the protocol of the targeted exchange:
The user interface of a device, for example, a keypad, screen or mouse) screens and take control of a control system. For an attack to succeed, an attacker needs to know the protocol of the targeted exchange:
Denial of service (DoS) attacks attempt to block legitimate access to network or device services. One common type of DoS attack floods a device with requests so that it's response times are slowed to the point where the system is unusable.
Another type of DoS attack floods the network with traffic, for example, Transmission Control Protocol synchronize (TCP SYN), affecting network response times to the point where legitimate use is severely impacted.
More than 75% of network-related system outages are attributed to accidental events. Causes of accidents can include poor network design, programming errors, improperly functioning network devices, non-compliance with procedures, or simply human error, for example, accidentally connecting network cables in wrong ports. Many of the security features and processes discussed in this document can also mitigate accidental events.
In many cases, contractors contribute directly to system design, commissioning, or maintenance. Operational procedures should be refined so that contractors cannot introduce malware or vulnerabilities into a control network![]() The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic. For example, you should automatically scan contractor equipment for malware infection before allowing access to any control network equipment. USB devices are another common source of malware infection and should be carefully screened before permitting their use.
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic. For example, you should automatically scan contractor equipment for malware infection before allowing access to any control network equipment. USB devices are another common source of malware infection and should be carefully screened before permitting their use.
Individuals who inadvertently connect a network cable into the wrong port on a multi-port switch can create outages or broadcast![]() Messages that are sent out to all devices on the network storms that can disable a network or severely affect its performance.
Messages that are sent out to all devices on the network storms that can disable a network or severely affect its performance.
In general, the cause might be accidental, but the features, practices and procedures used for cybersecurity work equally well against accidental system outages.
Whether an incident is an accident or a deliberate attack, preparation is key. Disaster recovery methods should be developed and tested so that recovery from an outage or other events can be quickly and reliably managed. High availability and redundant architecture play a role in this area when even a short system outage cannot be tolerated.
Last update - February 2026