Methods of Attack
This topic describes common methods of cyber-attack.
Select from the options below to display the details required:
Virtual Local Area Network (VLAN![]() An implementation in some managed Ethernet switches to group ports and nodes based on IEEE 802.1Q tags. This allows isolating network traffic and reduces Ethernet collision domains, resulting in better performance and deterministic system behavior) hopping is a method of attacking networked resources on a VLAN. The attacker uses switch spoofing or double-encapsulated frames on an unauthorized port to gain access to another VLAN.
An implementation in some managed Ethernet switches to group ports and nodes based on IEEE 802.1Q tags. This allows isolating network traffic and reduces Ethernet collision domains, resulting in better performance and deterministic system behavior) hopping is a method of attacking networked resources on a VLAN. The attacker uses switch spoofing or double-encapsulated frames on an unauthorized port to gain access to another VLAN.
Common types of attacks carried out once the intruder has gained access to the desired VLAN:
-
Media Access Control (MAC) flooding attack, confined to the VLAN of origin.
-
IEEE 802.1Q and Inter-switch Link (ISL) tagging attack.
-
Double-Encapsulated 802.1Q/nested VLAN attack.
-
Address Resolution Protocol (ARP) attacks.
-
Private VLAN attack.
-
Multicast brute force attack.
-
Spanning Tree Protocol (STP) attack.
-
Random frame stress attack.
Supervisory control and data acquisition (SCADA) systems may be vulnerable to Structured Query Language (SQL) Injection attacks. SQL injection is a code injection technique that occurs in the database layer of an application. An attacker executes unauthorized SQL commands by taking advantage of poorly secured code on a system connected to the internet. Vulnerable points include the log in and URL string.
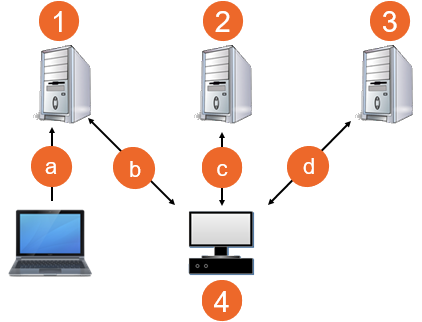
SQL injection attacks are used to steal information from a database and/or to gain access to an organization's host computers through the computer that is hosting the database:
|
|
Internet Protocol (IP) Spoofing is a method used to disguise the identity of an attacker attempting to perform malicious attacks such as denial of service and man-in-the-middle. IP spoofing is accomplished by manipulating the IP address.
IP is the main protocol used to communicate data across the internet. The IP header![]() The control information added to the beginning of a transmitted message. It contains required information, for example, the packet or block address, source, destination, message number, length and routing instructions. of the data contains the information necessary to transport data from the source to the destination. The header includes, but is not limited to:
The control information added to the beginning of a transmitted message. It contains required information, for example, the packet or block address, source, destination, message number, length and routing instructions. of the data contains the information necessary to transport data from the source to the destination. The header includes, but is not limited to:
-
Information about the type of IP datagram.
-
How long the datagram remains active on the network.
-
Special flags indicating any special purpose the datagram is supposed to serve, such as whether or not the data can be fragmented.
-
The destination and source addresses.
The receiver of a packet can identify the sender by the source IP address. In IP spoofing, the attacker manipulates the datagram, usually creating a false source IP address to hide their identity.
The primary motives of an attack are to:
-
Gather information about open ports, operating systems or applications on the host, for example, a port 80 response may indicate that the host is running a web server. Using Telnet, the attacker can see the banner and determine the web server type and version. The attacker can now try to exploit any vulnerability associated with that web server.
-
Uncover the sequence-number. Transmission Control Protocol (TCP) requires the use of a sequence number for every byte transferred and an acknowledgment from the recipient. An attacker can send several packets to the victim in an attempt to determine the algorithm. Once the algorithm is determined, the attacker tricks the target in to believing it is legitimate and launches attacks.
-
Hijack an authorized session by monitoring a session between two communicating hosts and injecting traffic that appears to be coming from one host. By doing so, the attacker steals the session from one host and terminating its session. The attacker continues the same session with the same access privileges to the legitimate host.
-
Bypass an Access Control List (ACL) security, start a Distributed Denial Of Service (DDOS) attack or hide the identity of attacker for diverse attacks such as sending illegitimate Modbus write requests.
Denial of Service (DoS) is an attempt to deny legitimate users access to a devices' services either temporarily or permanently. One common method involves saturating the victim's computer with external communication requests to either block responses or, respond so slowly that the system becomes ineffective. The attacker usually accomplishes this by:
-
Crashing the system.
-
Denying communication between systems.
-
Bringing the network or the system down or have it operate at a reduced speed affecting usability and productivity.
-
Hanging the system, more disruptive than crashing the system as there is no automatic reboot. Productivity can be disrupted indefinitely.
Last update - February 2026