Network Segmentation
Network segmentation is highly recommended for Process Control Networks and other mission-critical environments. It involves dividing the control network![]() The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic into logical segments and establishing security zones to limit the spread of threats. Network segments can be established using devices, for example, managed Ethernet, which provide virtual local area network (VLAN
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic into logical segments and establishing security zones to limit the spread of threats. Network segments can be established using devices, for example, managed Ethernet, which provide virtual local area network (VLAN![]() An implementation in some managed Ethernet switches to group ports and nodes based on IEEE 802.1Q tags. This allows isolating network traffic and reduces Ethernet collision domains, resulting in better performance and deterministic system behavior) and access control list management capabilities, firewalls and routers.
An implementation in some managed Ethernet switches to group ports and nodes based on IEEE 802.1Q tags. This allows isolating network traffic and reduces Ethernet collision domains, resulting in better performance and deterministic system behavior) and access control list management capabilities, firewalls and routers.
As a first level of defense, managed Ethernet switches can be configured to help protect every port from unauthorized access. Port access can be defined for specific Media Access Control (MAC) or Internet Protocol (IP) addresses.
Additionally, the rate limiter feature on switches can help reduce the likelihood of denial of service (DoS) and other flood attacks. The rate limiter allows you to specify the maximum amount of traffic allowed in or out of each port.
VLAN functionality can be used to further restrict traffic by segmenting the physical network into multiple logical networks.
Segmentation facilitates the establishment of security zones; a security zone can consist of one or more network segments. Traffic into and out of a zone is subject to a zone-specific set of rules, enforced, monitored and supported using devices, for example, industrial firewalls. The organization of zones can be influenced by many factors including function, location and security requirements, for example, a zone may consist of network segments and devices located near each other that serve a related functional task, whilst another network zone could contain devices that share a common set of security requirements.
Network segmentation and the establishment of security zones can help to:
-
Contain malware infections to one network segment.
-
Improve security by limiting node visibility.
-
Stop intruder scans at the network level before they reach a potential target system.
-
Limit the impact of a security breach on a network.
-
Restrict broadcasts
 Messages that are sent out to all devices on the network and multi-casts to particular VLAN.
Messages that are sent out to all devices on the network and multi-casts to particular VLAN. -
Improve network performance and reduce network congestion.
-
Control communication access between segments providing critical devices or systems get a higher level of security.
Virtual Local Area Networks (VLAN)
One common method of network segmentation is the use of virtual local area networks (VLANs). VLANs divide a physical network into smaller logical networks to increase performance, improve manageability, simplify network design and provide another layer of security. For example, separate VLANs could be established for each of the three device network security zones.
VLAN is an Open Systems Interconnection (OSI) Layer 2 broadcast domain![]() A collection of devices that receive broadcasts sent on an Ethernet network. The broadcast domain ends at a router positioned in the network. If any device in a broadcast domain broadcasts information, the information is received by all devices in the same domain. It is not received by devices connected through a router configured on managed switches on a port-by-port basis. Traffic on each VLAN segment is isolated from other VLANs, where the switch does not filter traffic between two devices on the same VLAN. VLANs can limit the impact of a security breach if a system in one becomes compromised.
A collection of devices that receive broadcasts sent on an Ethernet network. The broadcast domain ends at a router positioned in the network. If any device in a broadcast domain broadcasts information, the information is received by all devices in the same domain. It is not received by devices connected through a router configured on managed switches on a port-by-port basis. Traffic on each VLAN segment is isolated from other VLANs, where the switch does not filter traffic between two devices on the same VLAN. VLANs can limit the impact of a security breach if a system in one becomes compromised.
VLAN Guidelines
VLAN grouping strategies vary greatly, but common strategies include grouping by:
-
Functional or cell/area zone - Each VLAN carries only the traffic necessary for the operation of a particular cell/area zone.
-
Access requirements - VLANs are grouped according to the access requirements of different types of users, for example, operators, engineers or vendors.
-
Security - VLANs are grouped to support the control of access to sensitive information, devices and processes.
-
Traffic - VLANs are grouped to balance traffic loads in support of the required throughput.
Segmentation guidelines include:
-
Use one VLAN per ring topology for all manufacturing traffic per cell or area zone.
-
Use dedicated VLAN for device management, for example, switch or server.
-
Contain Voice over Internet Protocol (VoIP) on to a dedicated VLAN.
-
Assign a restricted VLAN identifier (ID) to packets entering the demilitarized zone (DMZ) from the enterprise network so those packets can access only specific devices in the DMZ.
-
Remove all unnecessary traffic from each VLAN.
-
Apply quality of service (QoS) access control lists (ACL) to rate-limit the amount of ping traffic allowed.
-
Avoid protocols that send passwords in clear text, for example, telnet and file transfer protocol (FTP). Use secure shell (SSH) and secure file transfer protocol (SFTP) sessions if the device supports those protocols. If Telnet or FTP is needed, use ACLs or firewall rules to allow connections only between specific hosts
 A node on a network, for example, a computer, that can be logged into and used interactively.
A node on a network, for example, a computer, that can be logged into and used interactively. -
Disable unused ports or put them into an unused or untrusted VLAN that has very restricted access.
-
Avoid the use of VLAN 0 transparent mode, as the packets are sent without VLAN membership.
Communication Between VLANs
Once a network is segmented into VLANs, users need restricted communications between the VLANs. This can be achieved by using a Layer 3 switch that combines the functionality of a router and a switch which can map traffic from one VLAN to another.
Firewalls
Firewalls help protect networks by permitting authorized access and blocking unauthorized access. A firewall is a device or set of devices configured to permit, deny, drop, encrypt, decrypt or proxy traffic between different security zones based upon a set of rules and other criteria. Additionally, firewalls can support event logging to a syslog server or to an internal event log in the firewall. Event logging is used to monitor security events and alarms that occur on an industrial network and can be used to identify network threats.
Typical events that can be monitored are:
-
Firewall interface up or down.
-
Attempted log-in to firewall.
-
Packets matching firewall rule allowed or denied.
-
Denied packets that do not match a rule.
-
Power failure or power recovery.
It is recommended to systematically store and then review event logs.
Process control devices require fast data throughput and often cannot tolerate the latency![]() The delay incurred by an Ethernet switching or bridging device between receiving and forwarding the frame introduced by an aggressive security strategy inside a control network. Firewalls play a role in a security strategy by providing levels of protection at the perimeters, or even within the network. A control system relies heavily on perimeter protection and network segmentation to block unwanted and unauthorized traffic.
The delay incurred by an Ethernet switching or bridging device between receiving and forwarding the frame introduced by an aggressive security strategy inside a control network. Firewalls play a role in a security strategy by providing levels of protection at the perimeters, or even within the network. A control system relies heavily on perimeter protection and network segmentation to block unwanted and unauthorized traffic.
Common firewall types include the following:
Select from the options below to display the details required:
A packet filtering firewall is a first-generation basic firewall that exerts minimal impact on network performance. Packets are filtered based on basic information in each packet, for example, Internet Protocol (IP) address, source and destination, and port number. Rules based on this information are established to determine if a packet is forwarded or dropped.
An application proxy gateway![]() A combination of hardware and software that interconnects incompatible networks or networking devices. Gateways include, packet assembler/disassembler and protocol converters firewall examines packets at the application layer and filters traffic based on rules that regulate access by applications, for example, browsers, or protocols for example, file transfer protocol (FTP). It also acts as a gateway for client requests, determining the final server address. Application proxy gateway firewalls provide a high level of security but can cause overhead delays that slow down network performance, this makes them suitable for systems located in the control room operations network, but not for the performance-sensitive networks of the control system.
A combination of hardware and software that interconnects incompatible networks or networking devices. Gateways include, packet assembler/disassembler and protocol converters firewall examines packets at the application layer and filters traffic based on rules that regulate access by applications, for example, browsers, or protocols for example, file transfer protocol (FTP). It also acts as a gateway for client requests, determining the final server address. Application proxy gateway firewalls provide a high level of security but can cause overhead delays that slow down network performance, this makes them suitable for systems located in the control room operations network, but not for the performance-sensitive networks of the control system.
A host![]() A node on a network, for example, a computer, that can be logged into and used interactively firewall is a software-based firewall that resides on a host device and protects its ports and services. Most laptops, servers and workstations feature integrated host firewalls. Host firewalls support the creation of customized rules to help protect particular ports and services; they are an important feature of laptops, mobile devices, engineering workstations and human machine interfaces (HMI
A node on a network, for example, a computer, that can be logged into and used interactively firewall is a software-based firewall that resides on a host device and protects its ports and services. Most laptops, servers and workstations feature integrated host firewalls. Host firewalls support the creation of customized rules to help protect particular ports and services; they are an important feature of laptops, mobile devices, engineering workstations and human machine interfaces (HMI![]() The user interface of a device, for example, a keypad, screen or mouse) in industrial networks.
The user interface of a device, for example, a keypad, screen or mouse) in industrial networks.
Stateful multilayer inspection firewalls combine the features of other firewall types. They:
-
Filter packets at the network layer and validate that the session packets and their contents at the application layer are legitimate.
-
Keep track of network connections, for example, Transmission Control Protocol (TCP) and User Datagram Protocol (UDP) connections that traverse the firewall.
-
Allow packets that match known good connections and rejects those that do not.
-
Inspect and check that inbound packets are the result of an outbound request.
Stateful inspection firewalls provide a high level of security, good performance and require less configuration effort.
Deep packet inspection firewalls, typically offer the same benefits as stateful firewalls but also offer the ability to interrogate and make forwarding![]() The process whereby an Ethernet switch or bridge reads the contents of a packet and passes it on to the appropriate attached segment decisions based on the analysis of application packets. These firewalls can block certain message types, control application traffic from specific hosts
The process whereby an Ethernet switch or bridge reads the contents of a packet and passes it on to the appropriate attached segment decisions based on the analysis of application packets. These firewalls can block certain message types, control application traffic from specific hosts![]() A node on a network, for example, a computer, that can be logged into and used interactively and help stop application traffic from flooding critical devices. A potential disadvantage of deep packet inspection firewalls is that they can have a greater negative impact on performance than stateful firewalls.
A node on a network, for example, a computer, that can be logged into and used interactively and help stop application traffic from flooding critical devices. A potential disadvantage of deep packet inspection firewalls is that they can have a greater negative impact on performance than stateful firewalls.
National Institute of Standards and Technology (NIST) Firewall Guidelines
The National Institute of Standards and Technology (NIST) published the following guidance in SP800-82 (Guide to Operational Technology (OT) Security):
-
By default, "deny all, permit none." (When defining explicit or implicit deny rules, Watlow Electric Manufacturing Company recommends implementing a drop action rather than a reject action. This prevents system interrogation from external sources.)
-
Ports and services between the control system network environment and the corporate network should be enabled and permissions granted on a specific case-by-case basis. There should be a documented business justification with risk analysis and a responsible person for each permitted incoming or outgoing data flow.
-
All "permit" rules should be both IP address and TCP or UDP port specific.
-
All rules should restrict traffic to a specific IP address or range of addresses.
-
Traffic should be prevented from transiting directly from the control network
 The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic to the corporate network. All traffic should terminate in a DMZ.
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic to the corporate network. All traffic should terminate in a DMZ. -
Any protocol allowed between the control network and the DMZ should explicitly NOT be allowed between the DMZ and corporate networks (and vice-versa).
-
All outbound traffic from the control network to the operations network should be source and destination-restricted by service and port.
-
Outbound packets from the control network or DMZ should be allowed only if those packets have a correct source IP address that is assigned to the control network or DMZ devices.
-
Control network devices should not be allowed to access the internet.
-
Control networks should not be directly connected to the internet, even if protected via a firewall.
Other Firewall Risk Mitigation Guidelines
Select from the options below to display the details required:
Packet filtering provides network security based on unique applications and protocols. It filters packets based on IP protocol and the packet source IP address, source port, destination IP address and destination port.
With packet filtering, access to a device can be restricted to allow only specific protocols (ports).
For example, the PC communicates with the PLC via port 80, but port 69 messages are blocked by the firewall:
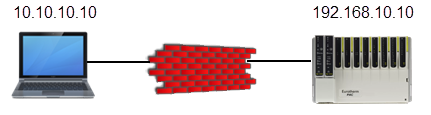
Access List
| System Integrator | Port | NOE Address | Port | Allow |
|---|---|---|---|---|
|
10.10.10.10 |
80 |
192.168.10.10 |
80 |
Yes |
|
10.10.10.10 |
69 |
192.168.10.10 |
69 |
No |
Ports that need extra protection due to inadequate built-in security include:
Non-Secure Protocols
| Application Protocol | Internet Protocol | Port Number | ||
|---|---|---|---|---|
|
Telnet |
TCP |
23 |
||
|
HTTP |
TCP/UDP |
80 |
||
|
SNMP v1 and v2 |
TCP/UDP |
161 |
||
| FTP |
TCP |
|
||
|
TFTP |
UDP |
69 |
||
|
DNS |
TCP/UDP |
53 |
||
|
POP3 |
TCP |
110 |
||
|
SMTP |
TCP/UDP |
25 |
||
|
Modbus TCP |
TCP |
502 |
Packet filtering should be implemented on incoming connections, untrusted ports, and on outgoing connections and trusted ports.
Some firewalls can inspect the protocol to make intelligent decisions about allowing or restricting specific messages. These firewalls can inspect a protocol, for example, Modbus TCP- port 502, and allow certain function codes to pass while blocking others.
Denial of service (DoS) attacks are a common form of flood attacks. If a DoS attacker penetrates a control network![]() The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic, the impact can be minimized using flood protection provided in a firewall. Flood protection within a firewall allows you to set limits on certain traffic types, for example, a high number of incoming or outgoing TCP connections per second that could indicate a DoS attack.
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic, the impact can be minimized using flood protection provided in a firewall. Flood protection within a firewall allows you to set limits on certain traffic types, for example, a high number of incoming or outgoing TCP connections per second that could indicate a DoS attack.
Last update - February 2026