Securing Operational Technology (OT) Systems and Defense in Depth
Watlow recommends a defense-in-depth approach to cybersecurity, as no single approach is deemed adequate. The defense-in-depth approach layers a network with security features, appliances and processes integrating a set of related process and systems components to provide higher levels of security in a plant network:
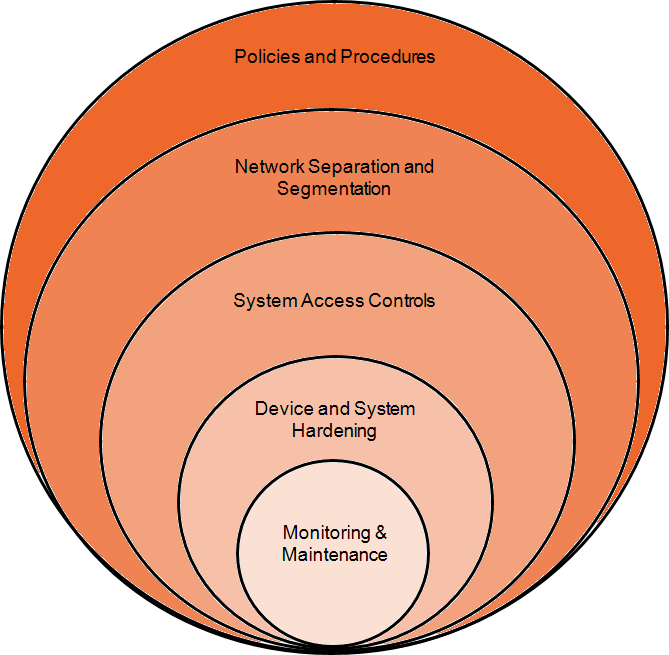
The basic components of a defense-in-depth approach are:
-
Policies and Procedures - A comprehensive set of policies and procedures which covers all aspects of cybersecurity, including but not limited to:
-
Training and cybersecurity awareness programs, these should include employees, sub-contractors and visitors.
-
Risk assessment, a systematic security analysis of the entire plant, including physical security, information technology (IT), operational technology (OT), network and infrastructure security.
See Risk Assessment for details. -
Security plans, built around the results of a security risk assessment, including business continuity plan if a security incident occurs and plans for deploying IT and OT network and infrastructure security.
-
-
Network Separation and Segmentation - Physical separation of the control network
 The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic from other networks using a demilitarized zone (DMZ) and the division of the control network itself into functional zones connected by secure conduits.
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic from other networks using a demilitarized zone (DMZ) and the division of the control network itself into functional zones connected by secure conduits. -
System Access Controls - Controlling physical access using traditional security measures, for example, perimeter defenses, for example, fences, locked gates and doors, closed-circuit television (CCTV), and logical access to the system using firewalls, authentication, authorization, virtual private networks (VPNs), anti-virus software and intrusion detection/prevention systems.
-
Device and System Hardening - This is the process of configuring devices, including PCs, servers, network security devices and control devices to aid in reducing the attack surface of the system. Device hardening measures include password management, access control, disabling of unused ports, services, applications and functionality.
See Device Hardening for details. -
Monitoring & Maintenance - An effective defense-in-depth campaign does not stop when security is implemented and deployed. Security and its constituent components require continual monitoring for unusual or unexpected behavior and maintenance, this includes patch management.
See Monitoring and Maintenance for details.
Last update - February 2026