Risk Assessment
Risk assessment is the process of analyzing and documenting a plant and related systems to identify and prioritize potential threats.
The goals of this phase are to:
-
Identify and document all potential threats.
-
Prioritize these threats according to severity, business impact and safety criteria.
-
Decide the order in which to address the threats and how to distribute resources to the effort.
An assessment examines possible threats from internal sources, for example, disgruntled employees and contractors, and external sources, for example, hackers and vandals. It examines potential threats to continuity of operation and assesses the value and vulnerability of assets, for example, proprietary recipes and other intellectual properties, processes and financial data.
The outcome of this assessment should be used to prioritize cybersecurity resource investments addressing the processes, devices and networks with the highest risk and highest business and safety implications.
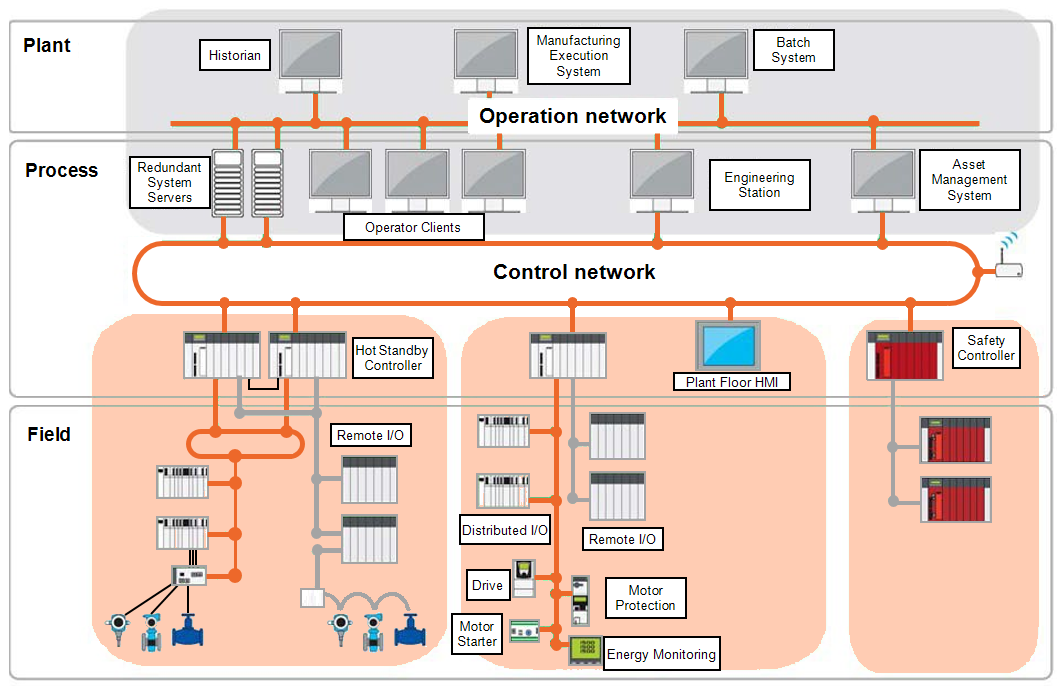
Infrastructure Diagrams
Infrastructure diagrams show a network infrastructure divided into logical segments and zones, and the conduits that connect them. They can help identify weaknesses, potential threats and origins of threats to devices and processes:
Security Plan
A security plan defines the policies on which the defense-in-depth implementation is based and the job and role specific procedures to execute those policies. Security policies and procedures define:
-
Roles and responsibilities of those affected by the policy and procedures.
-
Actions, activities and processes that are allowed and not allowed.
-
Consequences of non-compliance.
-
Incident response policies and procedures. These define the steps to take if a cyber-attack or accident occurs and should include:
-
Incident response plan - Who to notify and what actions to perform to contain the incident.
-
Incident recovery plan - Role-specific procedures for restoring devices and process to a known good operating state.
-
A security plan also details the equipment, software, protocols, procedures and personnel involved in implementing the components of a defense-in-depth program. It summarizes the findings of the risk assessment phase and includes detailed network diagrams and the training plan.
Develop and maintain a security plan with a team representing management, information technology (IT) staff, control engineering, operation and security experts and review the plan periodically for changes in threats, environment, and adequate security level.
Training Plan
Awareness plays an important role in the success of a defense-in-depth campaign and the development of a security conscious culture. Watlow recommends the establishment of a two-phase training program for employees and other agents.
-
Phase One - A cybersecurity awareness program that educates stakeholders on the organization's security policies, procedures, and standards. This is an ongoing program with update sessions given regularly.
-
Phase Two - Job and role-based training classes that detail the relevant security policies, procedures and standards that pertain to a particular job or function, these provide specific steps for applying the security policies and procedures. They also include specific instructions to follow if a cyber-attack or accident occurs.
Consider providing training classes for vendors, outside repair personnel and other visitors providing an overview of company security policies and procedures with a special emphasis on the privileges and restrictions that apply to the visitor.
Last update - February 2026