How Attackers Can Gain Access to your Control Network
A cyber attacker bypasses perimeter defenses to gain access to a control system network.
Common points of access include:
Select from the options below to display the details required:
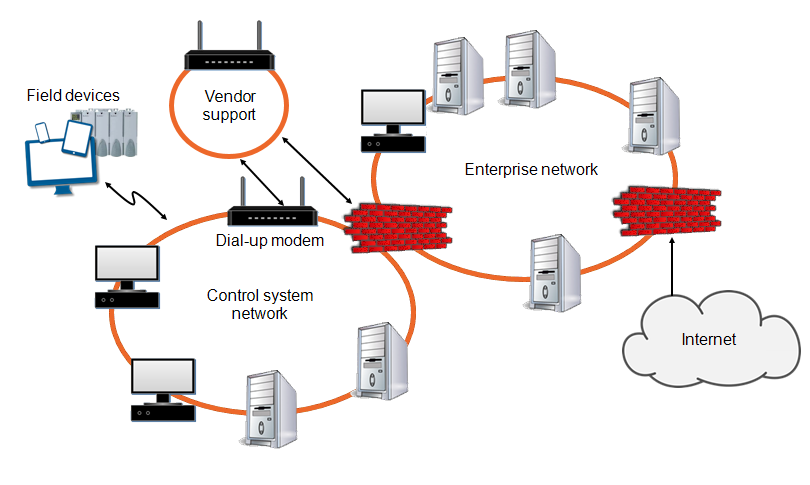
To reduce 'down time' and costs, organizations often grant access to suppliers for remote diagnostics or maintenance. This can be via remote access support applications, for example, LogMeIn, via a virtual private network (VPN), computers exposed to internet allowing the use of Teamviewer type of remote access or through dial-up modems. These suppliers sometimes leave ports open on the equipment to simplify their tasks, giving attackers access to the equipment and links to control system networks:
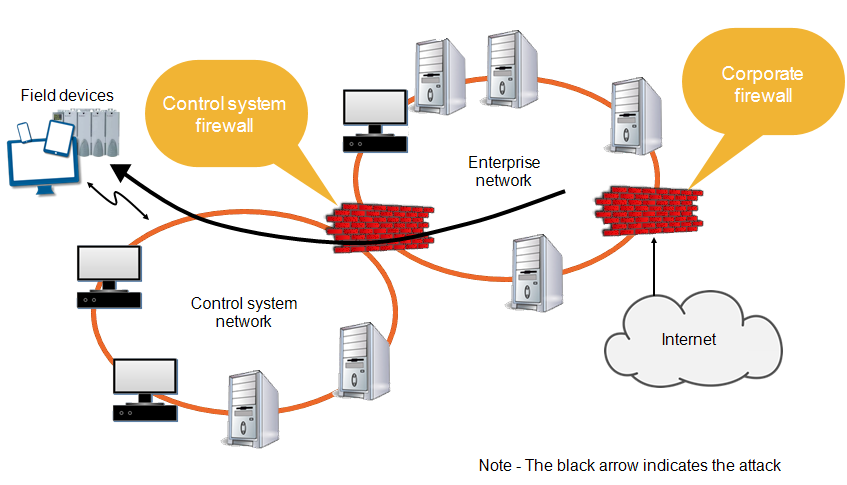
The automation department's network authority is often limited to the control network![]() The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic within a facility, and the Information Technology (IT) department assumes responsibility for the organization's long-distance communication. A skilled attacker can access a control network through the communication architecture and reconfigure or compromise communications to the field control devices:
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic within a facility, and the Information Technology (IT) department assumes responsibility for the organization's long-distance communication. A skilled attacker can access a control network through the communication architecture and reconfigure or compromise communications to the field control devices:
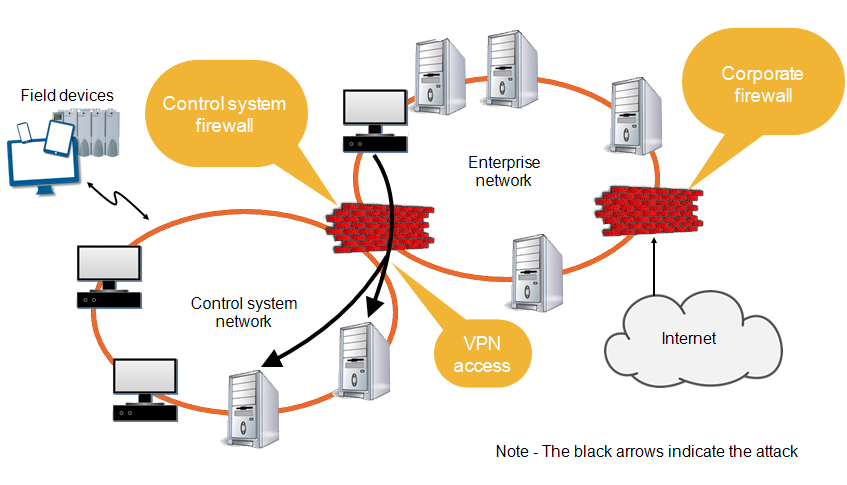
Engineers working in corporate offices often use virtual private network (VPN) connections to gain access to a control network![]() The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic. An attacker can compromise the VPN server, wait for a legitimate user to establish a VPN connection into the control system network and then piggyback onto a legitimate connection:
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic. An attacker can compromise the VPN server, wait for a legitimate user to establish a VPN connection into the control system network and then piggyback onto a legitimate connection:
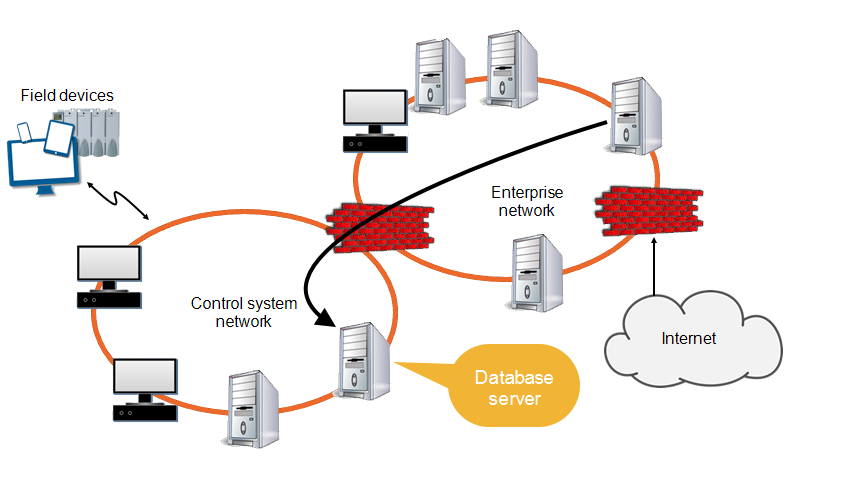
A majority of control systems use real-time databases, configuration databases and multiple historian databases. If the firewall, or the security of a database is not configured properly, a skilled attacker can gain access to the database from the business network and generate Structured Query Language (SQL) commands to take control of the database server on a control system network:
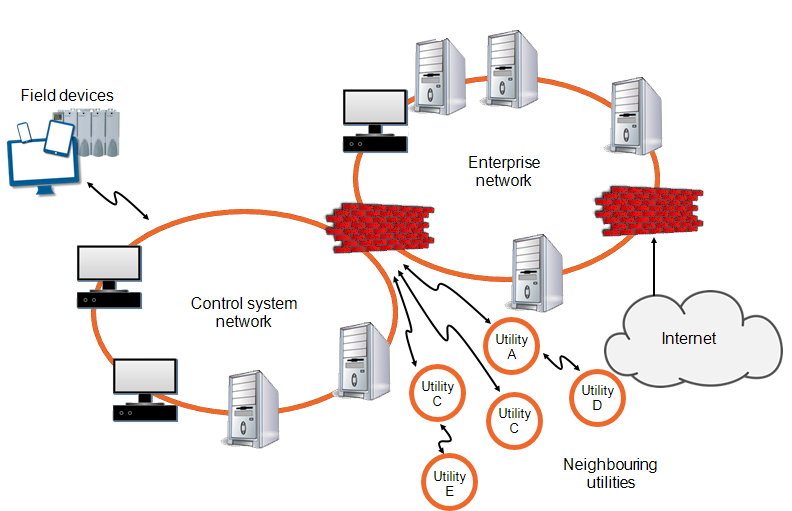
Partners and peers are sometimes granted access to information located on either the business or control network![]() The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic. With a peer-to-peer link, the security of a system is only as strong as the security of the weakest member:
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic. With a peer-to-peer link, the security of a system is only as strong as the security of the weakest member:
With the introduction of wireless communication (Wi-Fi) in industrial architecture, access to a network can be accomplished through any deployed access point. Implement proper configuration and physical security, especially in remote locations that are not monitored and where attackers would have the advantage of time to try to compromise an access point's security. It should be noted that where availability is essential, wireless is not a good choice as it is vulnerable to signal jamming denial of service (DoS) attack for which there is no countermeasure.
To address this challenge, use the newest available defense mechanisms and proper logging techniques to inform the network administrator about intrusion attempts.
A major component of network security is related to authorization and encryption. The initial security protocol, Wired Equivalent Privacy (WEP) has been declared obsolete since 2004. It was replaced by Wi-Fi Protected Access (WPA) and later by WPA2. Wireless networks are upgraded to support the newest security protocol, WPA2, which in the enterprise version supports Remote Authentication Dial-In User Service (RADIUS) server authentication mechanism. This way each client uses a different encryption key and along with the Advanced Encryption Standard (AES) encryption protocol is considered extremely difficult to hack.
If the WPA2 Pre-Shared-Key is used instead of the Enterprise version, the length and complexity of the key is the only effective defense against major attacks.
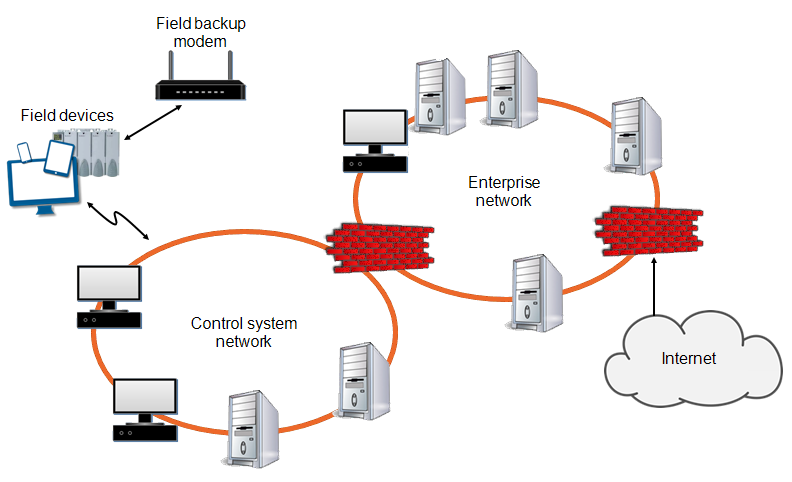
Many control systems have a backup Remote Terminal Unit (RTU) connection modem for use if the main network becomes unavailable. An attacker knowing the protocol of the RTU can gain access via dial-up. Most RTUs do not employ strong authentication or other security mechanisms, many accept and respond to any caller:
Last update - February 2026