Network Separation and the Demilitarized Zone
A firewall demilitarized zone (DMZ) separates industrial control networks![]() The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic from enterprise and other external communication paths. Bounded by a firewall the DMZ provides a security layer to help protect the control room's operations network and the deeper control and device networks:
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic from enterprise and other external communication paths. Bounded by a firewall the DMZ provides a security layer to help protect the control room's operations network and the deeper control and device networks:
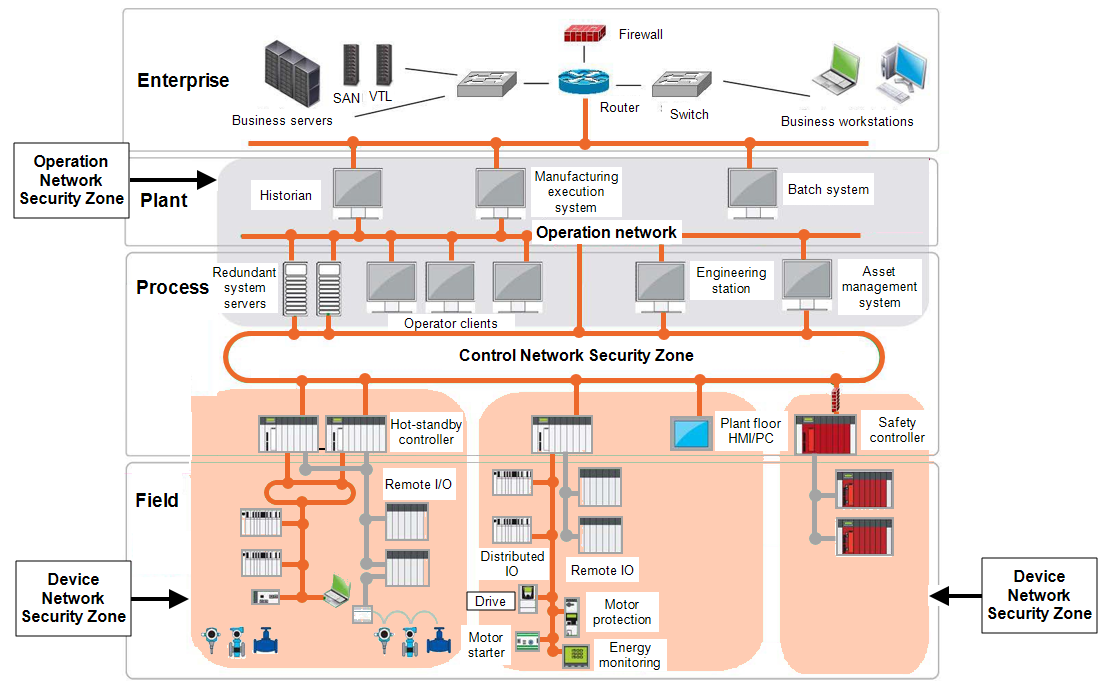
External requests and data terminate at controlled and dedicated servers and services within the DMZ. Requests and data from the control and operations networks terminate at servers and services in the DMZ. It allows no direct path of communication between the industrial control systems and the enterprise networks. For instance, industrial commands cannot travel from the enterprise to the control network![]() The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic, and industrial messages cannot travel from the control to the enterprise network.
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic, and industrial messages cannot travel from the control to the enterprise network.
Servers and services within the DMZ can include:
-
Data servers, for example, Historian that collect data from the supervisory control and data acquisition (SCADA) systems and share it with manufacturing execution systems (MES) or other reporting systems.
-
Patch management servers.
-
Proxy servers for web-connectivity or other protocols.
-
Remote authentication dial-in user service (RADIUS) and virtual private network (VPN) servers.
Some variations of the DMZ approach include a dedicated server or proxy within the DMZ to function as the sole conduit for communications between protected and external networks.
DMZ Guidelines
To provide higher levels of security with DMZs:
-
Filter inbound traffic to the control room through a firewall before allowing a connection to a server or service in the DMZ. Likewise, filter outbound traffic from the control room to external network. This traffic should be minimal and tightly controlled on a per protocol, per host and per user basis. Filter traffic destined to the control network
 The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic from the operations network. Filter traffic from the control network
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic from the operations network. Filter traffic from the control network The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic to the operations network. For example, multicast traffic should not enter or leave the control network
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic to the operations network. For example, multicast traffic should not enter or leave the control network The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic.
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic. -
Establish security policies limiting outbound traffic to required communications only. Devices on industrial control systems networks, including the operations, control, or device networks, should not have internet access.
-
Configure firewalls so that outbound traffic to the corporate network is source and destination restricted by service and port.
-
Configure firewalls to only accept Internet Protocol (IP) packets if they have a correct source IP address for the control network
 The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic, operations, or enterprise networks. Firewalls should drop any packet that comes in from the enterprise network with a source IP address that matches the address range of any of the control networks
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic, operations, or enterprise networks. Firewalls should drop any packet that comes in from the enterprise network with a source IP address that matches the address range of any of the control networks The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic. This scenario is indicative of a spoof or errant route.
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic. This scenario is indicative of a spoof or errant route. -
Harden servers in the DMZ. For examples of relevant server and client hardening methods, see Hardening Supervisory Control and Data Acquisition Systems for details.
-
Perform and document security patches and antivirus software updates on a monitored schedule.
Last update - February 2026