Communication Protocols and Port Usage Overview
This section describes how firewalls process and helps manage many of the protocols and services used in industrial control systems.
Select from the options below to display the details required:
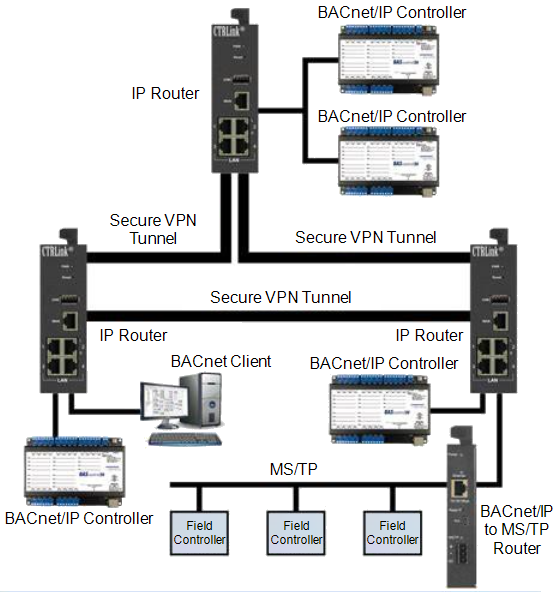
BACnet (Building Automation and Control Network) is a protocol used for building management systems (BMS) such as HVAC and lighting. BACnet/IP operates over User Datagram Protocol (UDP) port 47808. It enables peer-to-peer communication between controllers, sensors, and management stations.
Vulnerabilities
BACnet lacks native encryption and is susceptible to spoofing and replay attacks. Broadcast messages can be abused to discover and manipulate devices if the network is not segmented.
Risk Mitigation
Segment BACnet networks from IT systems using firewalls and VPN Tunnel. Use BACnet/SC (Secure Connect) with Transport Layer Security (TLS) encryption when supported. Disable foreign device registration and enforce strict access control lists (ACLs).
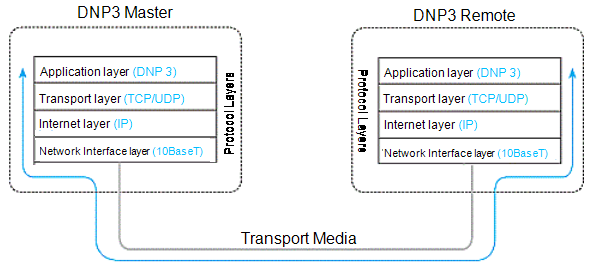
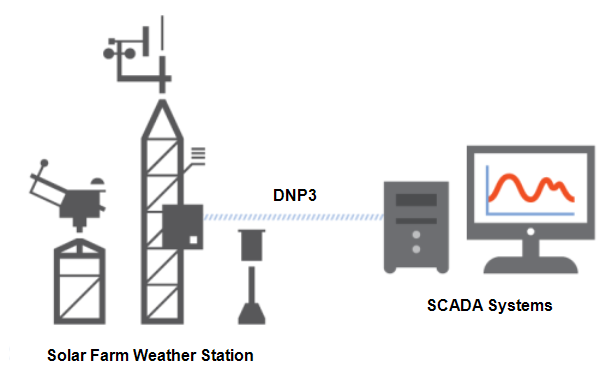
DNP3 (Distributed Network Protocol) is widely used in utilities and SCADA systems for telemetry and control. It provides reliable communication between master and outstation devices using port 20000/TCP or UDP.
Vulnerabilities
Legacy DNP3 lacks encryption and authentication, allowing potential command injection or data spoofing. Buffer overflow and replay attacks are also possible in older implementations.
Risk Mitigation
Implement DNP3 Secure Authentication (IEEE 1815-2012) to protect command integrity. Restrict DNP3 communications to specific subnets and use firewalls with DNP3 inspection capability. Monitor network traffic for abnormal control messages and unauthorized sources.
A domain name system (DNS) server is a database used to translate domain names to Internet Protocol (IP) addresses. Many internet services rely on DNS, but DNS is not commonly used by control systems. According to the National Institute of Standards and Technology (NIST), "In most cases there is little reason to allow DNS requests out of the control network![]() The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic to the corporate network and no reason to allow DNS requests into the control network.".
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic to the corporate network and no reason to allow DNS requests into the control network.".
Vulnerabilities
DNS servers are vulnerable to many exploits, including DNS cache poisoning and DNS amplification attack:
-
DNS cache poisoning is initiated by replacing the intended domain IP address with the attacker's domain IP address. Web traffic, e-mail and other network data can then be redirected to systems under the attacker's control.
-
DNS amplification attack is a type of denial of service (DoS) attack that generates traffic overload.
Risk Mitigation
-
Avoid DNS requests from the control network to the corporate network whenever possible, exceptions should be dealt with on a case-by-case basis.
-
Avoid allowing DNS requests into the control network.
-
If DNS is required, configure the firewall to use specific DNS servers instead of those allocated by an internet service provider (ISP).
Dynamic host configuration protocol (DHCP) is a network application protocol based on Bootstrap Protocol (BootP![]() Bootstrap protocol - A TCP/IP network protocol that lets network nodes request configuration information from a BootP server node). It is used by devices and DHCP clients, to obtain configuration information for operation in an Internet Protocol (IP) network. DHCP is an unauthenticated protocol which works by using the discover, offer, request and acknowledgment (DORA) grants:
Bootstrap protocol - A TCP/IP network protocol that lets network nodes request configuration information from a BootP server node). It is used by devices and DHCP clients, to obtain configuration information for operation in an Internet Protocol (IP) network. DHCP is an unauthenticated protocol which works by using the discover, offer, request and acknowledgment (DORA) grants:
|
|
DHCP service uses port 67/UDP in the DHCP server and port 68/UDP in the DHCP clients.
Vulnerabilities
There are two common types of DHCP attacks:
-
DHCP starvation attack - The DHCP server is inundated with requests from different media access control (MAC) addresses. The DHCP server eventually runs out of IP addresses blocking legitimate users from obtaining or renewing their IP addresses.
-
DHCP rogue attack - The attacker disguises itself as a DHCP server, responds to a DHCP request with false IP addresses, and then launches a man-in-the-middle attack.
Risk Mitigation
Allow only authorized persons to have physical or wireless access to the device. If DHCP is not needed, disable it in the firewall or any device supporting DHCP.
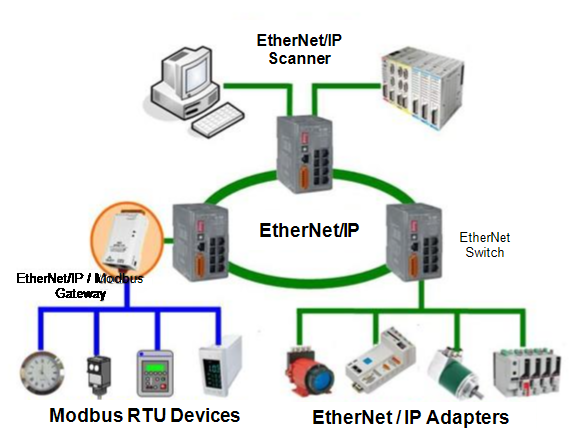
EtherNet/IP uses TCP port 44818 for explicit messaging and UDP port 2222 for implicit I/O.
Vulnerabilities
Because EtherNet/IP is built on TCP/UDP, it inherits traditional IT vulnerabilities such as spoofing, DoS, and replay attacks. It lacks inherent encryption or authentication, leaving devices exposed if deployed on flat or unsegmented networks.
Risk Mitigation
Implement industrial firewalls with CIP awareness to filter and inspect EtherNet/IP commands. Use VLANs or separate network conduits for control and safety-critical communications. Enable CIP Security extensions (TLS-based) where supported for mutual authentication and data integrity.
File Transfer Protocol (FTP) and Trivial File Transfer Protocol (TFTP) are used for transferring files between devices. TFTP is a simplified unidirectional protocol commonly used for special purpose file transfers, for example, the transmission of boot files between devices.
Watlow ethernet devices use FTP/TFTP for various tasks including, but not restricted to:
-
Firmware loading.
-
Displaying custom web pages.
-
Retrieval of logs and historical data files.
Vulnerabilities
FTP has the following vulnerabilities:
-
FTP uses a login password that is not encrypted.
-
TFTP requires no authentication.
-
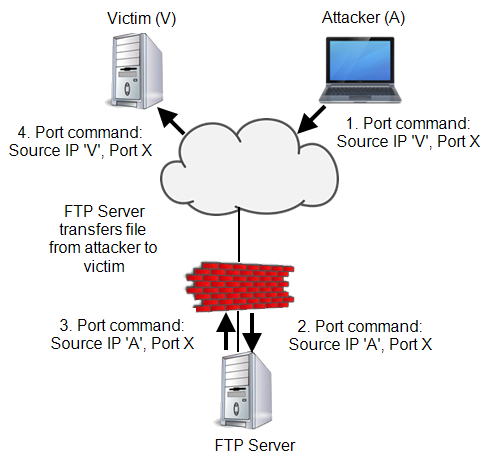
FTP is vulnerable to buffer overflow and FTP Bounce attacks:
-
Bounce attacks - These use an FTP server in passive mode to transmit information to any device on the network. To begin the bounce attack, the attacker logs into the middleman FTP server and once connected, they send the PORT command to direct all data connections to the illegitimate destination IP address and TCP port:
-
Buffer Overflow - A Buffer Overflow is a common anomaly in programming and information security where a program writes data to a buffer, exceeding the buffer's allocated memory. This can lead to overwriting adjacent memory locations, causing erratic program behavior, memory access errors, incorrect results, and crashes.
-
Risk Mitigation
To help mitigate FTP vulnerabilities, allow FTP communications for outbound sessions only unless they are secured with additional token-based multi-factor authentication and an encrypted tunnel:
-
If possible, use more secure protocols, for example, Secure File Transfer Protocol (SFTP), File Transfer Protocol Secure (FTPS) or Secure Copy (SCP).
-
Configure each server connection individually.
-
Use packet filtering to allow access only to the FTP server.
-
Block TFTP communications if they are not required.
Hypertext transfer protocol (HTTP) is the underlying protocol used by the world wide web (WWW). In control systems it supports embedded web servers in control products:
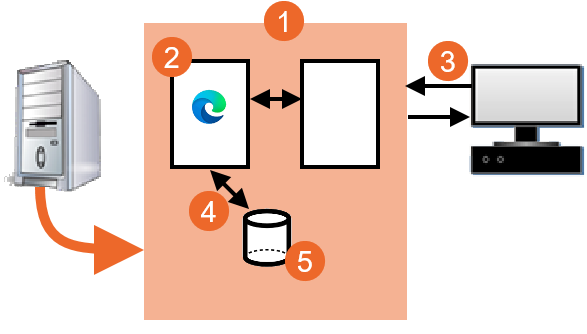
|
|
Hypertext transfer protocol secure (HTTPS) is a combination of the HTTP and a cryptographic protocol. By default, HTTP uses port 80 and HTTPS uses port 443.
HTTPS transmits normal HTTP with encryption, commonly using either transport layer security (TLS) or its predecessor, secure sockets layer (SSL).
Vulnerabilities
HTTP has little inherent security and can be used as a transport mechanism for attacks and worms. Common attacks are man-in-the-middle and eavesdropping.
Risk Mitigation
If an HTTP server is not required, disable it. Otherwise, use HTTPS instead of HTTP if possible and only allow traffic to specific devices.
Internet Control Message Protocol (ICMP) is used for network diagnostics (ping, traceroute) and error reporting. It operates at the network layer and does not use ports.
Vulnerabilities
ICMP can be used for reconnaissance or denial-of-service attacks, for example, ping floods, Smurf attacks. It may also be used for covert data exfiltration.
Risk Mitigation
Limit ICMP to diagnostic purposes within internal networks. Block or rate-limit ICMP echo requests from external sources. Monitor ICMP traffic for anomalies and disable unused message types.
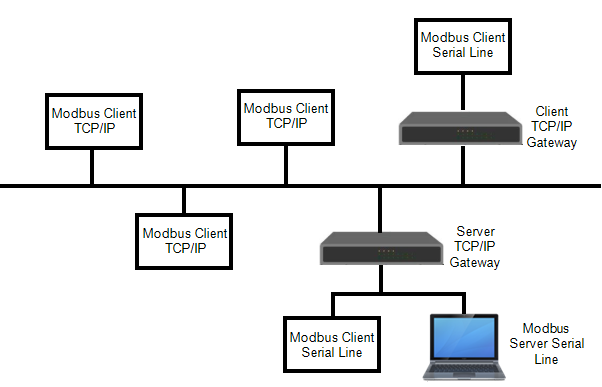
Modbus is one of the most widely used industrial communication protocols, developed originally by Modicon. It enables communication between supervisory systems and field devices over serial (RTU) or Ethernet (TCP) connections. Modbus TCP typically uses port 502. In Operational Technology (OT) environments, Modbus provides cyclic polling-based data exchange for process monitoring and control, often between Programmable logic controllers (PLCs), Human Machine Interfaces (HMIs) and Supervisory Control and Data Acquisition (SCADA) servers. Its simplicity and openness also make it vulnerable when exposed to untrusted networks.
Vulnerabilities
Modbus lacks built-in encryption or authentication, allowing any host on the network to issue valid commands. Attackers can exploit this to perform replay attacks, modify process variables, or cause denial of service. Because Modbus transmits in clear text, it is susceptible to packet sniffing and man-in-the-middle attacks.
Risk Mitigation
Restrict Modbus traffic to control zones only and never route it to enterprise networks. Use deep packet inspection firewalls with Modbus protocol awareness to enforce command and register whitelisting. If remote access is required, tunnel Modbus TCP through VPN or TLS encryption. Segment Modbus devices into secure conduits per IEC 62443 zone model and apply least-privilege access principles.
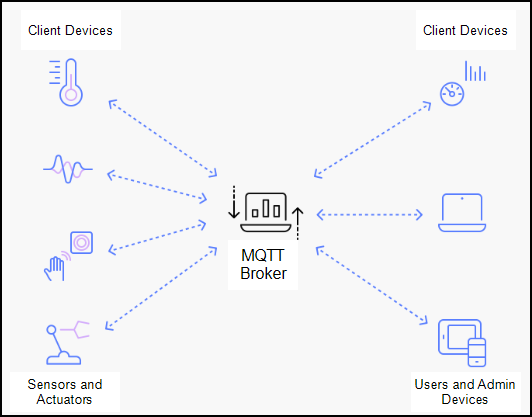
Message Queuing Telemetry Transport (MQTT) is a lightweight publish/subscribe messaging protocol used in Industrial Internet of Things (IIoT) and edge applications. It operates over TCP port 1883 or 8883 (with TLS).
Vulnerabilities
MQTT brokers can be exploited for unauthorized data publishing or subscription if authentication is weak. Unencrypted sessions can expose sensitive telemetry data to interception.
Risk Mitigation
Use TLS-secured MQTT (port 8883) with client certificate authentication. Restrict topic access via ACLs and segregate IIoT networks from critical control traffic. Monitor MQTT broker logs for abnormal connection attempts.
Network Address Translation (NAT), also known as Internet Protocol (IP) masquerading, is a service that conceals a device's true IP address from the outside world to keep outside agents from accessing the device directly. IP addresses used on one side of a network device are mapped to a different set on the other side:
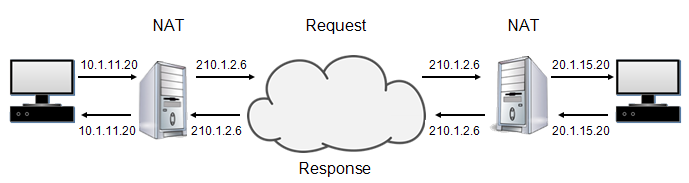
NAT maps the entire network to a single IP address prior to transmitting; it relies on the premise that not every internal device is actively communicating with external hosts at any given moment. The NAT device tracks the state of each connection and how each private internal IP address and source port was remapped. When the response is received by the NAT device, the IP address mapping reverses and the packets forwarded to the appropriate internal host.
Although NAT routers are not firewalls, because they do not filter the packets, they do offer devices a level of protection from external networks. NAT does not allow inbound packets that were not sent in response to a request from accessing devices directly.
NAT technology was introduced to slow the advance of IP address space depletion and not as a security mechanism, when incorporating it the use of private IP addresses is possible for devices that need to communicate over the internet. As a side effect, NAT does conceal the true IP address of a device to the outside world, however, it does not conceal the internal architecture, and it should not be used as a security mechanism.
Vulnerabilities
None known.
Industrial Firewall Network Address Translation Features
NAT features supported by Industrial firewall include:
-
1:1 NAT can be used when setting up identical internal production cells that use the same IP addresses but need to be connected to an external network. The firewall replaces the source IP address of a data packet from the internal network with an IP address of the external network.
-
Inverse 1:1 NAT allows devices in an internal network to communicate with devices in an external network as if the devices in the external network were in the internal network. With inverse 1:1 NAT, the firewall replaces the destination IP address of a data packet from the internal network with an IP address of the external network.
-
Double NAT allows devices in an internal network to communicate with devices in an external network as if the devices in the external network were in the internal network and vice versa. To devices in the:
-
Internal network, the firewall allocates a different IP address in the external network (1:1 NAT function).
-
External network, the firewall allocates a different IP address in the internal network (inverse 1:1 NAT function).
-
-
NAT-IP Masquerading hides the internal network structure (IP addresses) from an external network. The firewall replaces the source IP address of a data packet from the internal network with the external IP address of the firewall.
-
NAT Port-Forwarding
 The process whereby an Ethernet switch or bridge reads the contents of a packet and passes it on to the appropriate attached segment hides the internal network structure from the outside but allows a communication connection to be set up from the outside in. External devices can set up a communication connection to the internal network and send data packets to a specific port with the external IP address of the firewall.
The process whereby an Ethernet switch or bridge reads the contents of a packet and passes it on to the appropriate attached segment hides the internal network structure from the outside but allows a communication connection to be set up from the outside in. External devices can set up a communication connection to the internal network and send data packets to a specific port with the external IP address of the firewall.
Network Address Translation Configuration Recommendations
-
Use NAT whenever possible.
Note - NAT does not support producer-consumer protocols, for example, Ethernet/IP or Foundation Fieldbus. -
Since NAT is usually used on routers and network gateways
 A combination of hardware and software that interconnects incompatible networks or networking devices. Gateways include, packet assembler/disassembler and protocol converters, its use requires enabling IP forwarding so that packets can travel between networks.
A combination of hardware and software that interconnects incompatible networks or networking devices. Gateways include, packet assembler/disassembler and protocol converters, its use requires enabling IP forwarding so that packets can travel between networks.
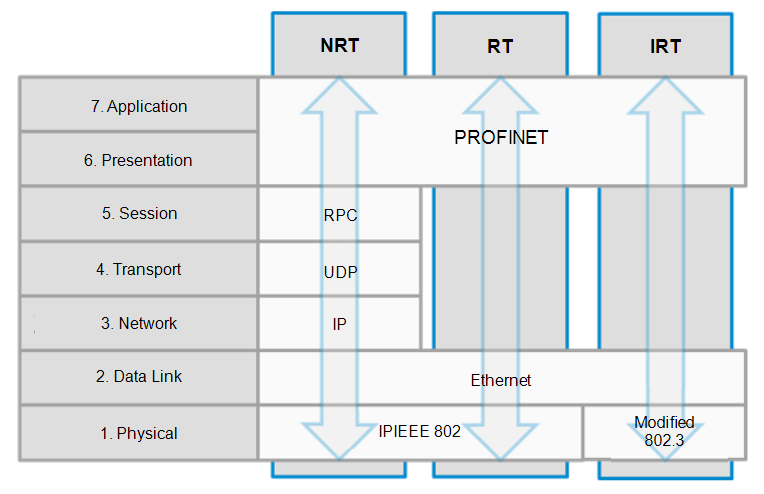
PROFINET uses Layer-2 Real Time (RT) frames (EtherType 0x8892) for cyclic I/O. TCP/UDP (port 34964) are used only for non-real-time services such as configuration.
Vulnerabilities
PROFINET does not include inherent encryption or strong authentication. Improper segmentation can allow attackers to send unauthorized control frames or disrupt communication using broadcast storms or ARP spoofing.
Risk Mitigation
Ensure PROFINET traffic is isolated within the control zone. Disable unused ports and enable switch port security. Use industrial switches supporting PROFINET conformance class C/D with security profiles and integrate with intrusion detection systems.
Open Platform Communications (OPC) Classic
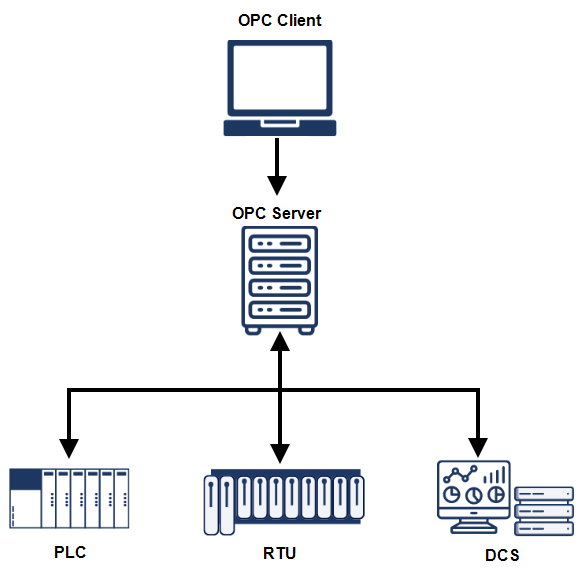
OPC Unified Architecture (UA)
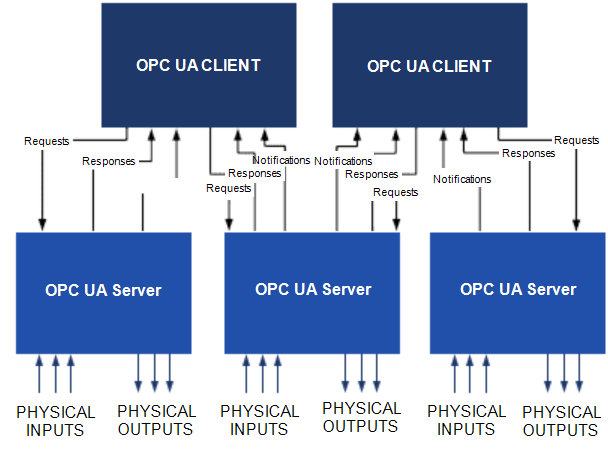
OPC (Object Linking and Embedding (OLE) for Process Control) is a set of standards for data exchange between control systems and applications. OPC Classic uses DCOM, while OPC UA (Unified Architecture) provides a platform-independent, service-oriented model with built-in security. Typical ports: 135 (DCOM), 4840 (OPC UA).
Vulnerabilities
OPC Classic relies on Windows DCOM, which exposes systems to authentication and privilege escalation risks. OPC UA improves security, but misconfiguration may still lead to weak certificate handling or unauthenticated endpoints.
Risk Mitigation
Migrate from OPC Classic to OPC UA wherever possible. Use signed and encrypted sessions in UA with X.509 certificates. Restrict OPC endpoints by IP and require user-level authentication. Harden Windows hosts used for Classic OPC with least privilege policies. Where migration is not yet feasible, consider using OPC tunnelling solutions to encapsulate Classic OPC traffic securely and eliminate direct DCOM exposure.
Secure communication protocols provide confidentiality, integrity, and authentication for data exchange across networks. SSL and its successor TLS encrypt communication for HTTPS, FTPS, and other services. SSH and SFTP use asymmetric cryptography to protect remote access and file transfers.
Common ports associated with secure communication include:
-
HTTPS: 443/TCP
-
SSH: 22/TCP
-
SFTP: 22/TCP
-
FTPS: 990/TCP or 21/TCP (implicit/explicit)
-
SMTPS: 465/TCP
-
IMAPS: 993/TCP
-
POP3S: 995/TCP
Vulnerabilities
Outdated versions such as SSLv2, SSLv3, and TLS 1.0/1.1 are no longer secure and are vulnerable to attacks like POODLE and BEAST. Weak cipher suites and improper certificate validation can undermine encryption effectiveness.
Risk Mitigation
Use only TLS 1.2 or TLS 1.3 for encrypted sessions. Implement SSH key-based authentication and disable password logins. Apply certificate management policies, including revocation and renewal. Restrict access to encrypted management interfaces via jump hosts or VPNs.
Email notification in the automation industry is more prevalent as plants increasingly rely on off-site personnel to troubleshoot issues. Watlow ethernet devices send and on occasion receive e-mail. Anti-virus software should be used to scan any received e-mails for viruses.
Email clients should not be enabled on any dedicated control room workstation or server, if receiving email is required, it should be received on dedicated business machines connected to the enterprise network.
The Simple Mail Transport Protocol (SMTP) is an internet standard used by e-mail clients or mail transfer agents (MTA) to send e-mails.
SMTP performs two functions, it:
-
Verifies that the configuration is valid and grants permission to the computer sending the message.
-
Sends the outgoing message to a predefined destination and validates the successful transfer of the message. If the message is not successfully transferred, a message is sent back to the sender.
Either Post Office Protocol v3 (POP3) or Internet Message Access Protocol (IMAP) are used by local e-mail clients to download e-mail from a remote server. The POP3 server receives the e-mail message and retains it until it is retrieved by the local client using port 110:

Vulnerabilities
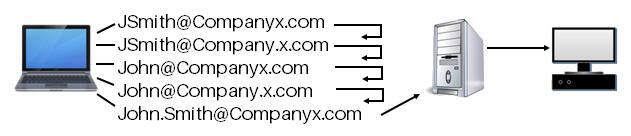
Directory harvesting is a common form of e-mail attack. The attack relies on invalid e-mail addresses being rejected by the e-mail system either during the SMTP conversation or afterwards via a Delivery Status Notification (DSN). An attacker sends an email and providing there is no rejection or delivery status notification (DSN) received, the e-mail address is considered valid and is added to a spam database. The two most common harvesting methods of attack are:
-
Brute force - An approach that sends messages with all possible alphanumeric characters.
-
Selective - An approach sending to likely username in hopes of finding a valid one:
Risk Mitigation
To help mitigate SMTP and POP3 risks:
-
Avoid allowing inbound e-mail to any control network
 The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic device.
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic device.
-
Allow outbound e-mail only when necessary, for example, a device may send an alert by e-mail so that would be a case where it is required.
Simple Network Management Protocol (SNMP) provides network management services between a central management console and network devices, for example, routers, printers and Production Activity Controls (PACs).
SNMP consists of three parts:
-
Manager - An application that manages SNMP agents on a network by issuing requests, getting responses and listening for and processing agent-issued traps.
-
Agent - A network-management software module that resides in a managed device. The agents allow configuration parameters to be changed by managers. Managed devices can be any type of device, including, but not limited to, routers, access servers, switches, bridges, hubs, PACs and drives.
-
Network management system (NMS) - The terminal through which administrators can conduct administration tasks.
Vulnerabilities
SNMP is considered to have weak security:
-
Versions one and two (v1 and v2) of SNMP use unencrypted community names to both read and configure devices. Community names may not be able to be changed.
-
Version three (v3) is more secure but is still limited.
It is often automatically installed with 'public' as the read string and 'private' as the write string. This type of installation provides an attacker the means to perform reconnaissance on a system to create a denial of service, see Denial of Service for details.
SNMP also provides information about the system that may allow the attacker to piece together the network system with the interconnection.
To help mitigate SNMP risk:
-
Where possible, deactivate SNMP v1 and v2 and use SNMP v3, which encrypts passwords and messages.
-
Change the default passwords of devices that support SNMP.
-
Block inbound and outbound SNMP traffic at the boundary of the enterprise network and operations network of the control room.
-
Filter SNMP v1 and v2 commands between the control network
 The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic and operations network to specific hosts or communicate with them over a separate, secured management network.
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic and operations network to specific hosts or communicate with them over a separate, secured management network. -
Control access by identifying which IP address has privilege to query an SNMP device.
-
If SNMP v1 or v2 is required, use access settings to limit the devices (Internet Protocol (IP) addresses) that can access the switch. Assign different read and read/write passwords to devices.
SNTP synchronizes clocks of networked devices with a time source, essential for accurate event logging in ICS. It uses UDP port 123 and provides simplified time synchronization based on NTP.
Vulnerabilities
SNTP lacks authentication, allowing spoofed time responses that can disrupt logs and alarms. Man-in-the-middle attacks can shift device time to obscure forensic data.
Risk Mitigation
Restrict SNTP requests to trusted time servers. Use authenticated NTP where available. Block inbound SNTP traffic from external networks and monitor for abnormal time adjustments.
The Teletype Network (Telnet) protocol provides interactive, text-based communications between a client and a host. Telnet provides access to a command-line interface, typically via port 23. It is mainly used for remote log in and simple control services to systems with limited resources or to systems with limited needs for security. As Telnet introduces a severe security risk, Watlow recommends disabling Telnet service in legacy products and replacing it with Secure Shell Protocol (SSH).
Vulnerabilities
All Telnet traffic, including passwords, is unencrypted, this allows a potential attacker considerable control over a device.
Risk Mitigation
To help mitigate Telnet risks:
-
Inbound Telnet sessions from corporate to control networks
 The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic should be prohibited unless secured with authentication and an encrypted tunnel, for example, a VPN tunnel.
The portion of the control system network where process data is transferred, including Supervisory Control and Data Acquisition
(SCADA) to Programmable Automation Controller (PAC) traffic and PAC to PAC traffic should be prohibited unless secured with authentication and an encrypted tunnel, for example, a VPN tunnel. -
Outbound Telnet sessions should only be allowed over encrypted tunnels to specific devices, see Remote Access Control with Virtual Private Network (VPN) for details.
-
Managed switches provide the option to disable the Telnet interface. Disable the Telnet interface when not using the command line interface to configure the switch.
Last update - February 2026